How Wuna Wallet Empowers Users with Secure Digital Identity Control
A secure digital identity wallet built for under-documented and remote communities — putting individuals in control of what they share, with whom, and when.
-
Client
- Project type Mobile App
- Industry Identity Verification
.png?length=400&name=WUNA%20(1).png)
Wuna Wallet is a web-based platform designed to help individuals — particularly from under-documented and remote communities — securely manage and share their identity and important documents.
Instead of identity being stored across disconnected systems, Wuna Wallet places ownership directly in the hands of the user.
The platform supports both individuals and service providers by enabling:
- secure digital identity storage
- real-time verification
- controlled document sharing
- and culturally safe identity validation
This creates a more direct and transparent way to manage identity — one that travels with the user.
Where Identity Breaks Down
Before Wuna Wallet, identity was something people constantly had to prove — often without the right tools or access.
Documents Are Lost Or Inaccessible
Many individuals didn’t have reliable access to their IDs, resumes, or certificates when they needed them most.
Verification Is Manual And Repeated
Limited Digital Access In Remote Areas
Lack Of Control Over Personal Data
Individuals had little visibility or say in how their data was used or shared.
You often have to prove who you are — again and again — before anything can move forward.
Trust, Culture, and Control
Building Wuna Wallet required more than just technical execution — it required trust.
- “How do we create a system people feel safe using?”
- “How do we ensure identity can be shared without losing control?”
- “How do we respect cultural identity while meeting modern system requirements?”
The challenge was to design a platform that:
-
simplifies access
-
protects user data
-
and aligns with cultural and community expectations

Identity on Your Terms
Wuna Wallet transformed identity from something fragmented into something portable and controlled.
Users can now store their documents, verify their identity, and share information directly from a single platform.
Service providers can access verified information instantly — without needing to repeatedly request documents or rely on manual processes.
Verify in seconds, share only what's needed
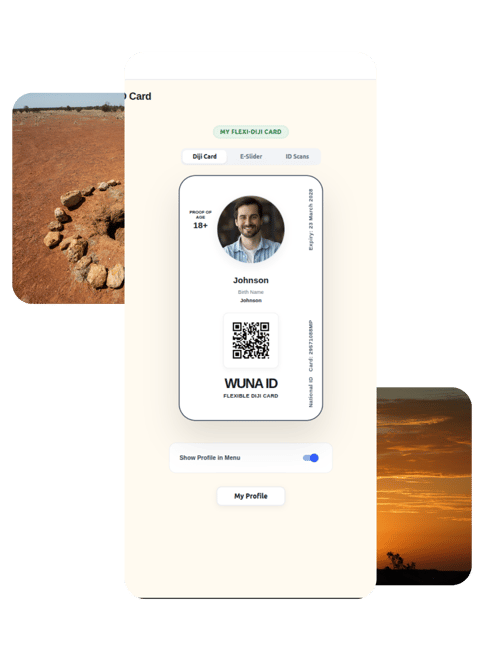
Users can generate a QR code to verify their identity in real time during interactions with services.
Document sharing is fully controlled by the user — they decide what is shared, with whom, and when.
This shift creates confidence on both sides of the interaction.
“We used to spend a lot of time chasing documents and verifying information. Now everything we need is in one place, and it’s much easier to support our clients.”
Designed for Real Access
The platform was designed to work across mobile, tablet, and web environments — ensuring it can be used in both remote and in-person settings.
QR-Based Identity Verification
Controlled Document Sharing
Culturally Safe Identity Framework
Decentralised Data Ownership
Compliance and Transaction Tracking
Seamless Access Across Devices
Building Trust Where It Matters Most
01 Designing for low-connectivity environments The platform needed to remain accessible in remote areas with limited digital infrastructure.
02 Establishing trust in a new identity system Users needed confidence that their personal data was safe, respected, and controlled by them.
03 Balancing compliance with cultural safety The system had to meet regulatory requirements while respecting cultural identity practices.
04 Supporting multiple user types Individuals, service officers, and institutions all interact with the platform differently — and all needed to feel supported.
Three principles that shaped the build
Designed from real-world challenges
Secure and user-controlled
Culturally informed approach
Respecting identity, community, and trust throughout the design.
Control That Travels With You
“I had to rely on others to prove who I am.”
“I can carry my identity with me and decide how it’s used.”
Individuals moved from fragmented, inaccessible identity processes to a system where they can securely manage and share their own information.
Service providers shifted from manual verification to instant, user-controlled access.
This created a more respectful and efficient exchange — where trust is built through transparency, not repetition.

Identity stopped being something you have to prove.
Now, it’s something you own — and carry with you.
Hey! Got a project?
Your project's type
What are the next steps?
- Our sales team reaches you within a few hours to organise a FREE consultation.
- Meanwhile, we sign an NDA to ensure the highest privacy level and protection of your idea.
- We will conduct a FREE consultation to understand your business requirements and will answer any questions you may have.
- Our expert strategist presents project estimates and approximate timelines.